Checking the Network DNS traffic for the last 24 hour I noticed that DNS amplification attacks are becoming very common. DNS is just one of the protocols that attackers use to send amplification attacks to target IPs. Additional to DNS, there are additional protocols (SSDP, NTP, SNMP,..) that are vulnerable to reflection/amplification attacks. An attacker can easily use the address spoofing method to remotely send an attack using a botnet network. Consequences of a DDOS attack against an enterprise can be dire, from financial costs to a negative impact on a brand’s reputation.

Facts about DDOS
- Most of the attacks are ~1Gbps of traffic, but as we can see in the traffic graph there is an attack that is ~17Gbps. Depending on you Internet connectivity, an attack of >1Gbps is enough to cause service disruption.
- DDOS attacks are no longer a matter of it companies will get hit, it’s now a question of how often and how long.
- Attacks are becoming bigger. Check what happened to Github back on Feb 28th
- An attacker can anonymously pay for for a DDOSER service for $24 a month or less. The more money, the more larger and destructive botnet network. Some options iddos.net, str3ssed.me, critical-boot.com.
- Some DDOS attacks (Not volumetric) can be identified and mitigated with on premise UTMs/WAFs. But if the attack is larger that your Internet bandwidth, any security device is useless.
Notes and protection options for enterprise customers
- On premise firewalls, IPS, IDS, WAF, UTM are useless for volumetric attacks.
- Firewalls and IPs are stateful devices, which often means they become target of DDoS attacks
- If possible avoid Email/DNS servers on premise. There are multiple cloud providers that you can use for this purpose.
- If you host web applications, consider using Cloud providers and CDN services. Multiple options available depending on the type of content, bandwidth, geography, etc:
- Make sure that your service provider can help with volumetric attacks and that you have complete control to trigger the protection. Some service providers provide an on demand service where protection is triggered as soon as an attack is detected or you can manually trigger it using a web portal or a BGP community.
- Use an on demand protection service of your service provider. An always on solution in your service provider cloud, usually degrades latency.
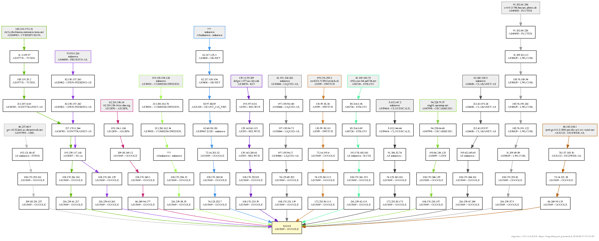
- Deploy internal traffic analysis tools using netflow/sflow/ipfix. The protocol will depend on the type of gear that you use in your network. Multiple open source and commercial options are available. Some options:
- Avoid GRE based DDOS solutions. It has several disadvantages like:
- Tunneling usually degrades performance.
- The DDOS solution provider advertise the subnet via BGP using their own ASN.
- If a single host in your network is under attack, you have to protect a whole /24.
- When your traffic is being protected, the latency of your apps will increase.
- Triggering the protection usually takes time > 20-30 minutes and you will depend completely on the service provider.
- Visibility and analytics tools are important. Understanding where traffic is going and coming can help you to proactively detect and mitigate a DDOS attack.
Factors to consider for Service providers
- Make sure that you have a blackhole BGP community deployed and that you test the community with every single transit and peering provider.
- Real time analytics of your traffic is important. Even if you have a large sampling in the flow export, you will be able to detect volumetric attacks.
- Deploy automatic protection methods. If an attack is detected have automatic ways to send the attacked IP to a scrubbing center or send it to blackhole
- A DDOS attack can cause service disruption in a complete metro market.
- Have a plan for scenarios where the attacked IP is an IP of one of your core routers.
- Deploy software based/SDN traffic injection and rerouting. Avoid GRE based solutions if possible.
- Consider using BGP Flowspec. You will have more mitigation options
Whether you face DDOS attacks of 1Gbps+, 10Gbps+ or 100Gbps+ work on a plan. It’s a matter of time.